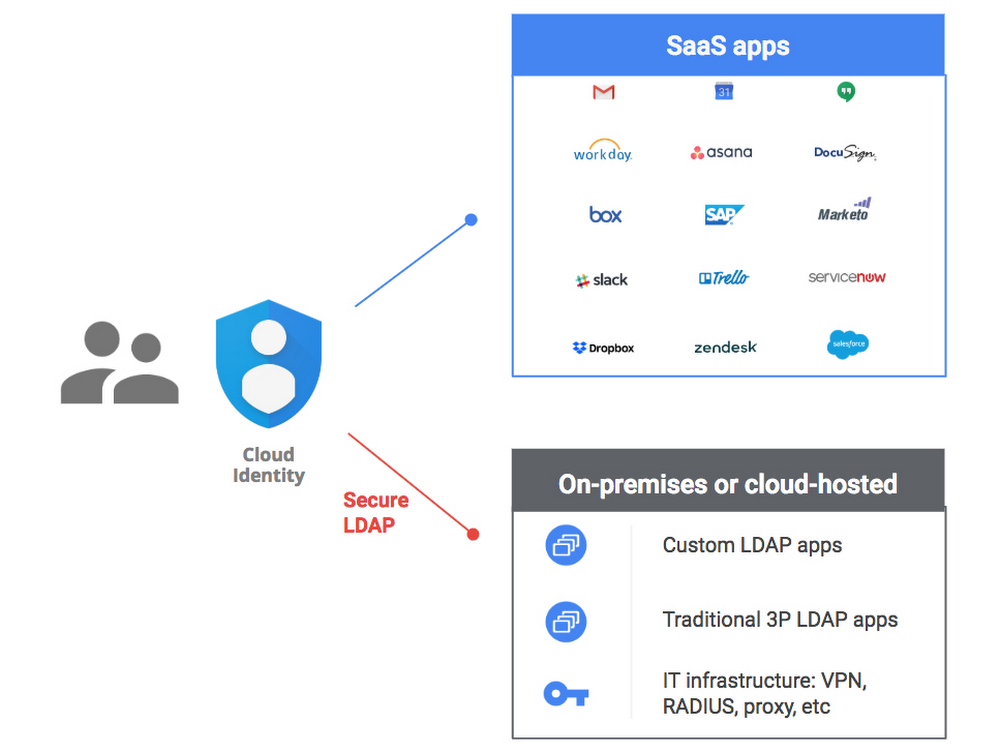
Google just released Secure LDAP functionality to Google Workspace for Education domains. This opens the door to many significant changes and opportunities for schools and districts. Coupling this with the new custom password policies, Google Workspace can now offer a viable alternative to on-premise LDAP providers like AD or eDirectory.
LDAP settings can be found under Apps in your Google Admin console.

What Google Workspace Secure LDAP means for you
Many districts we work with rely on an on-premise LDAP provider like Active Directory. We have seen a trend moving away from AD as a whole, but many districts still rely on it for authentication. Logging in to Windows PCs, SIS platforms, application software, etc are great reasons to keep AD around — until now.
Google Workspace Secure LDAP lets you connect any service or application that uses LDAP authentication to your Google Workspace domain. Instead of users logging in with their AD credentials, Google Workspace credentials can be used.
Successfully transitioning to Google Workspace for authentication for all of your cloud, web, and local services can have big implications down the road. We see this as a final step to removing dependency on Active Directory, but what else can we reduce? User provisioning options can be drastically simplified — many districts we work with use large scale identity management solutions to provision to many destinations. Removing AD completely means you can potentially provision directly to Google Workspace from your SIS. If you can fully move to Secure LDAP, you can potentially remove all the physical and virtual infrastructure require to maintain an AD environment.
Learn more about optimizing your OU structure
Moving to Google Workspace Secure LDAP
Amplified IT has been participating in the Secure LDAP Trusted Tester program for a few months. We have been working with Google engineers on the Secure LDAP team, providing feedback and testing various situations. We have been successful in logging in to both Windows and Linux PCs with our Google Workspace account credentials! We were able to decouple our Windows Server VMs running in Google Compute Engine from our Active Directory domain, connect them to Google Workspace Secure LDAP, and remote desktop in using a Google Workspace username & password.
Windows authentication is likely a big challenge when moving off AD and to Secure LDAP. Touching every Windows PC on a network will be difficult, but we’ve been testing a few solutions. We can automate connecting an individual PC to Secure LDAP. We’re actively testing connecting a Windows AD Primary Domain Controller to Secure LDAP, so all clients can stay exactly as they are. We’ve successfully tested connecting a Windows PC to a Linux VM, which is set to authenticate to Secure LDAP as a proxy. There are a lot of possibilities, and we’re seeing great success so far.
Aside from Windows authentication, research will be required to identify all of your AD authentication dependencies. You can slowly roll out Secure LDAP as you identify tools and apps which rely on LDAP for authentication. Once you have one system connected to Secure LDAP, the process will be familiar enough to make it easy to roll out. If you use a AD for GPO or software deployment, consider upgrading to Windows 10 or similar to take advantage of MDM.
If you’re fully invested in ADFS, SSO, or other solutions, Secure LDAP might not make sense for your environment. If you’re eager to remove your dependency on AD or another local LDAP provider, you should evaluate what Secure LDAP can do, and compare that to what you need. Considering savings on AD management tools, on premise VMs and physical servers required to host that environment, and ease of user management are all good reasons to look at Secure LDAP as a low-cost alternative.
UPDATE: We’re no longer helping people spin up Secure LDAP in favor of the newer Windows Management, Read about the change to Windows device management here.
We’re no longer helping people spin up Secure LDAP in favor of the newer Windows Management. Read about the change to Windows device management here.
Find this article useful? Share it!
-

Keegan Morrison
Chief Cloud Architect -
About the Author:
Keegan lives in Chesapeake, VA and works at Amplified IT’s home office in Norfolk where he leads the Technical Services team. Keegan received his Bachelor’s degree from Old Dominion University in Computer Science and started work as a Linux Systems Administrator fresh out of college. When he isn’t working, he likes hiking and kayaking, spilling wood glue on his flannel shirts while attempting to build things in his workshop, photography, and astronomy, and teaching his son animal noises instead of language. His favorite food is dark chocolate and his favorite drink is a hoppy West coast style IPA.